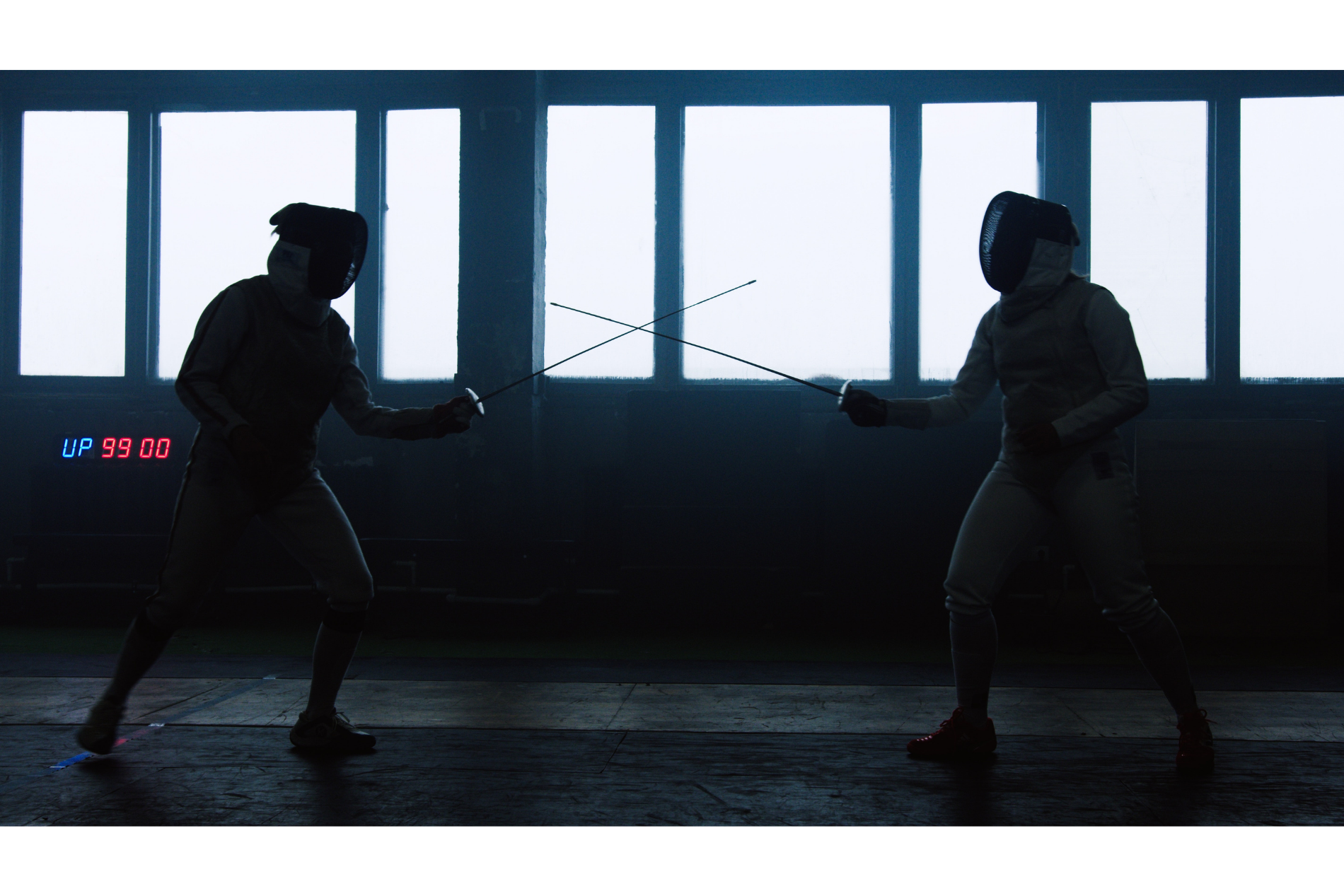
We’re going to break all rules of blog articles here, and start by talking about something that isn’t IT security, stick with us – it’s important!
When is a door not a door?
When it’s a way of letting criminals in to bypass your multi-million-pound security system.
Let us explain….
We recently came across a story online, of a business that hired someone to try and penetrate their new, incredibly expensive security system. Not only did they manage it, but it didn’t take them very long, and they did it in broad daylight right under the noses of security staff and security-conscious employees.
How? They relied entirely on people’s default nature to be polite and follow the rules.
Initially, they gained access to the business premises by smashing a van window from a distance, allowing them to be casually waved on through security in a van branded with the details of a windscreen repair company. This doesn’t seem entirely unreasonable, given that they were expected and who else would know the screen was broken?
They pretended to look at the screen and declared it to be unfixable and left. In the time that took, someone had got out of the van, and put a sign on the building exit saying ‘Please leave this door open’. When it was hometime, the first person read it and propped the door open, and no one else questioned it. Again, not too unreasonable – it’s a secure site, and why else would there be a sign on the door if there wasn’t a good reason?
Once everyone had gone, that person was allowed to walk straight through the open door, completely bypassing the expensive system without touching it, and solely relying on people’s assumptions, and human nature to be polite.
How does this relate to IT security?
Phishing scams and online scams, in general, are getting more and more sophisticated. The clever ones aren’t the ridiculous emails from far-flung princes offering you your inheritance as the rightful heir to the throne, they’re the ones that pray on human traits and emotions. Capitalising on a human willingness to do the right thing, their panic at the suggestion that their emails have been hacked, or their desire to follow instructions from their boss.
IT security isn’t just about tech. We wish there was something you could purchase and be 100% secure from online threats – the worst part of our job is helping to clear up after a hacking attempt has been successful.
The best way to protect your business is to take a layered approach to security. Utilise the tech options open to you, but also take into consideration staff training. Get your IT provider to carry out some dummy hacking attempts to see where the training is needed, so no one is wasting their precious workday learning what they already know. This is so important, as an IT provider, we actually offer comprehensive staff training as part of our IT offering, to help you avoid letting cybercriminals waltz right in and wreak havoc in your business. You can learn more about the security services we provide here.